In order to create a flawless product, it needs to undergo unparalleled quality assurance and testing.
One of the preliminary testing techniques to understand the fundamental behavioral output of a system or application is black box testing. It aims to identify the functioning of the application such as usability, response time, and reliability, and categorize them under expected or unexpected outcomes.
A powerful testing technique, it exercises a system end-to-end.
This blog will help you understand black box testing in detail, including its various techniques and tools used.
What is Black Box Testing?
Black box testing is a software testing technique where testers do not have access to the internal code or structure of the system being tested. Instead, testers focus on the software from the perspective of an end-user, testing for input/output behavior, usability, and software functionality. It helps to ensure that the software meets the user's requirements, and also helps to identify potential bugs and errors that could harm the functionality of the software. This type of testing is crucial in ensuring that software is reliable and good quality for end-users.
Let’s understand with an example, suppose you are testing a website's search functionality. You know that users should be able to enter a search term and receive a list of results related to that term. You do not know how the search algorithm works, but you can test its functionality by entering different search terms and observing the results.
Black Box Functional Testing Technique
Black box testing has various techniques that are used to test the functionality of an application. It is important to understand the concepts of each of these techniques to understand which one is the right for your project. Let’s take a look at some of the most commonly used black box testing techniques
- ECP technique
Equivalence class partitioning (ECP) is a software testing technique that helps to identify test cases by dividing input data into equivalent classes. The goal of ECP is to reduce the number of test cases needed to achieve maximum test coverage while still providing effective testing.
The basic premise of ECP is that input data can be divided into different categories or classes based on their equivalence. For example, if a system accepts input values in the range of 50 to 90, input values can be divided into the following equivalence classes:
- Valid input values - Input values within the range of 50 to 90 are considered valid input values and belong to this equivalence class.
- Invalid input values - Input values outside the range of 50 to 90 are considered invalid input values and belong to this equivalence class.
- Null input values - Input values that are empty or null are considered null input values and belong to this equivalence class.
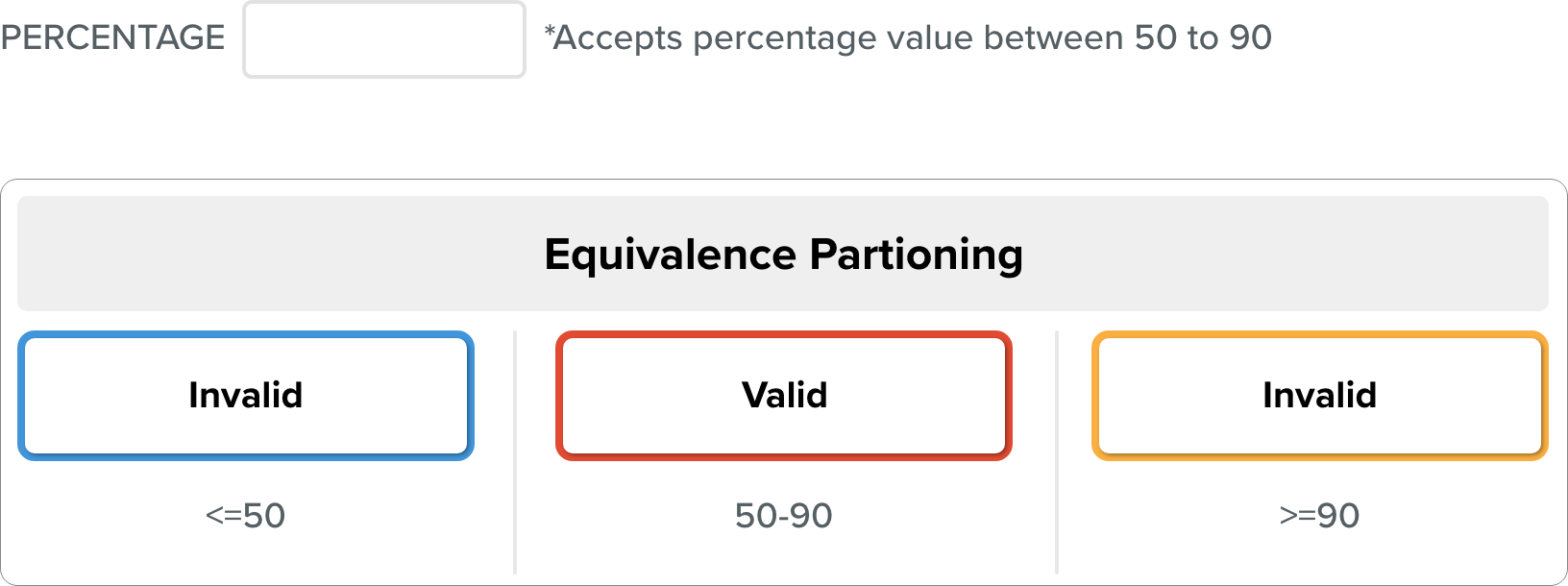
By dividing input data into these equivalence classes, testers can identify a set of representative test cases that can effectively test the system. For example, a test case can be created for each equivalence class to ensure that the system handles each type of input correctly.
The Equivalence class represents or defines a set of valid or invalid states for each input after it has been validated.
The requirements and specifications of the software serve as the basis for this technique. The benefit of this strategy is that by going from an infinite to a finite number of test cases, it helps to shorten the testing period. It is appropriate for use at every stage of the testing procedure.
Let's look at one instance:
Let’s consider, a feature of the software application that takes a cellphone number with 10 digits.
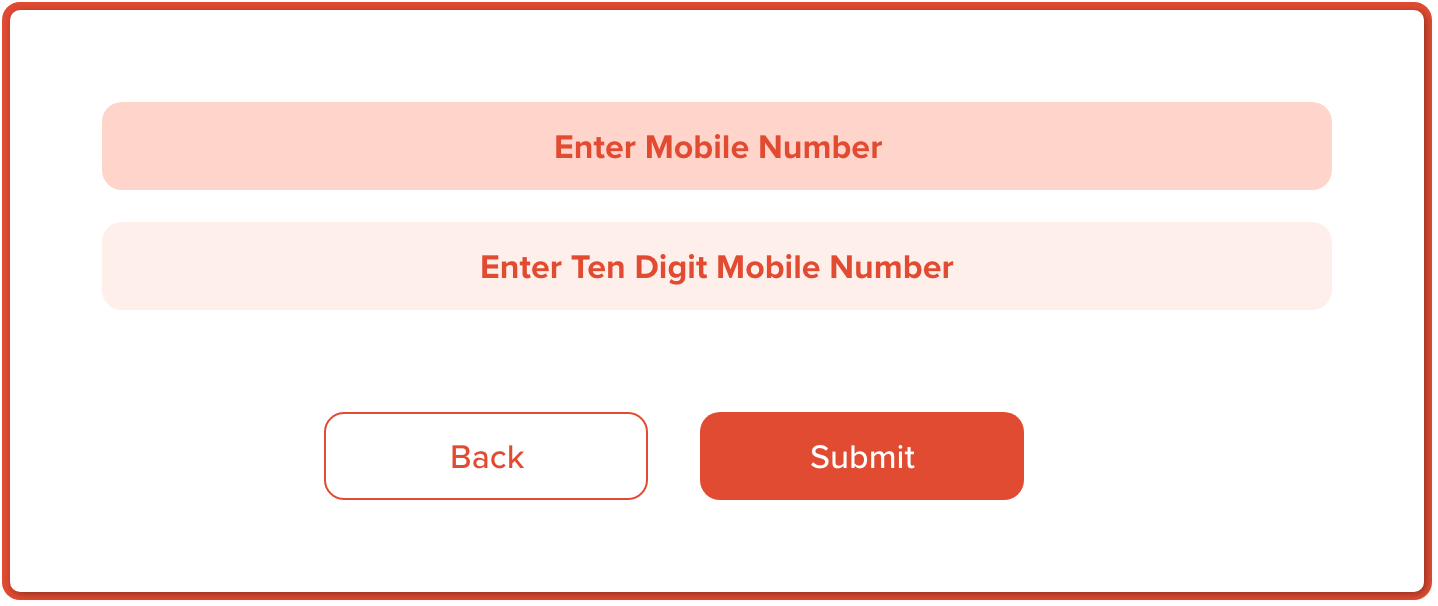
|
Invalid 1 Test Case |
Invalid 2 Test case |
Invalid 3 Test case |
Valid |
|
DIGITS>=11 |
DIGITS<=9 |
DIGITS=10 |
DIGITS=10 |
|
98472622191 |
984543985 |
9991456234 |
9893451483 |
With a mobile number of 10 digits as an example, we can observe that there are two equally legitimate and invalid partitions. The valid partitions operate the same way, which is to redirect to the next page.
In the example above, two further partitions include erroneous values of 9 or fewer than 9 and 11 or more than 11 digits. When these invalid values are applied, these invalid partitions behave similarly and are forwarded to the error page.
The above example shows that there are only three test cases, which is consistent with the equivalence partitioning principle, which states that this technique aims to reduce the number of test cases.
The benefit of the ECP Testing Technique
There are several benefits to using the ECP testing technique:
- Increased accuracy: ECP can detect errors that might be missed by other testing techniques increasing the overall accuracy of the testing process.
- Easy to implement: The ECP testing technique is not difficult to implement, and it can be used with a variety of platforms and software.
- Improved efficiency: ECP can save time and effort by quickly identifying invalid input and reducing the need for manual testing.
- Cost-effective: As compared to other testing methods, ECP is a cost-effective solution for software testing.
- Reduction of production issues: ECP testing helps to identify issues early on in the software development process, reducing production issues and making it easier to fix problems before they become costly mistakes.
Overall, the ECP testing technique is a powerful tool for detecting errors and improving software quality.
- Boundary Value Analysis Technique
Boundary value analysis is a software testing technique that focuses on testing the input values at the boundary or edge of the acceptable input range for a system or application. It is a type of black box testing that helps to identify errors or defects in the software that might be caused by boundary conditions.
The basic premise of boundary value analysis is that errors often occur at the extreme boundaries of the input values, rather than in the middle of the input range. By testing these boundary values, testers can identify potential errors and improve the quality of the software.
For example, let's consider a system that accepts input values in the range of 1 to 100. To perform boundary value analysis on this system, the tester would focus on testing the following input values:
- Minimum value- Testing the input value of 1, which is the minimum value in the acceptable range, helps to ensure that the system handles the smallest input value correctly.
- Maximum value- Testing the input value of 100, which is the maximum value in the acceptable range, helps to ensure that the system handles the largest input value correctly.
- Values just below the minimum- Testing input values just below the minimum value, such as 0 or -1, helps to ensure that the system handles values outside the acceptable range correctly and provides appropriate error messages.
- Values just above the maximum- Testing input values just above the maximum value, such as 101 or 1000, helps to ensure that the system handles values outside the acceptable range correctly and provides appropriate error messages.
- Decision Table Technique
The Decision Table Testing software testing approach is used to examine how the system responds to various input combinations. This methodical technique tabulates the various input combinations and the resulting system behavior.
Because the decision table records the causes and consequences of thorough test coverage, it is also known as a Cause-Effect table. Techniques such as decision table testing, which tests two or more inputs with a logical relationship, are frequently used.
There are multiple rules in the table for a single decision. A decision table's rules can be created by simply inserting AND between conditions.
In the below example, you will understand, how different input combinations, provide different results. Here “AND” is detonated by the sign of circumflex (^), Y stands for “Yes” and N stands for “No”. R1 to R4 stands for different conditions under certain input and outputs.
The following are the major rules that can be extracted (taken out) from the table:
- R1 = If (working-day = Y) ^ (holiday = N) ^ (Rainy-day = Y) Then, Go to the office.
- R2 = If (working-day = Y) ^ (holiday = N) ^ (Rainy-day = N) Then, Go to the office.
- R3 = If (working-day = N) ^ (holiday = Y) ^ (Rainy-day = Y) Then, Watch TV.
- R4 = If (working-day = N) ^ (holiday = Y) ^ (Rainy-day = N) Then, Go to picnic.
As per below graph, There is no need to check the condition in R1 and R2. If the day is working, whether it is sunny or rainy, the decision is to go to the office.
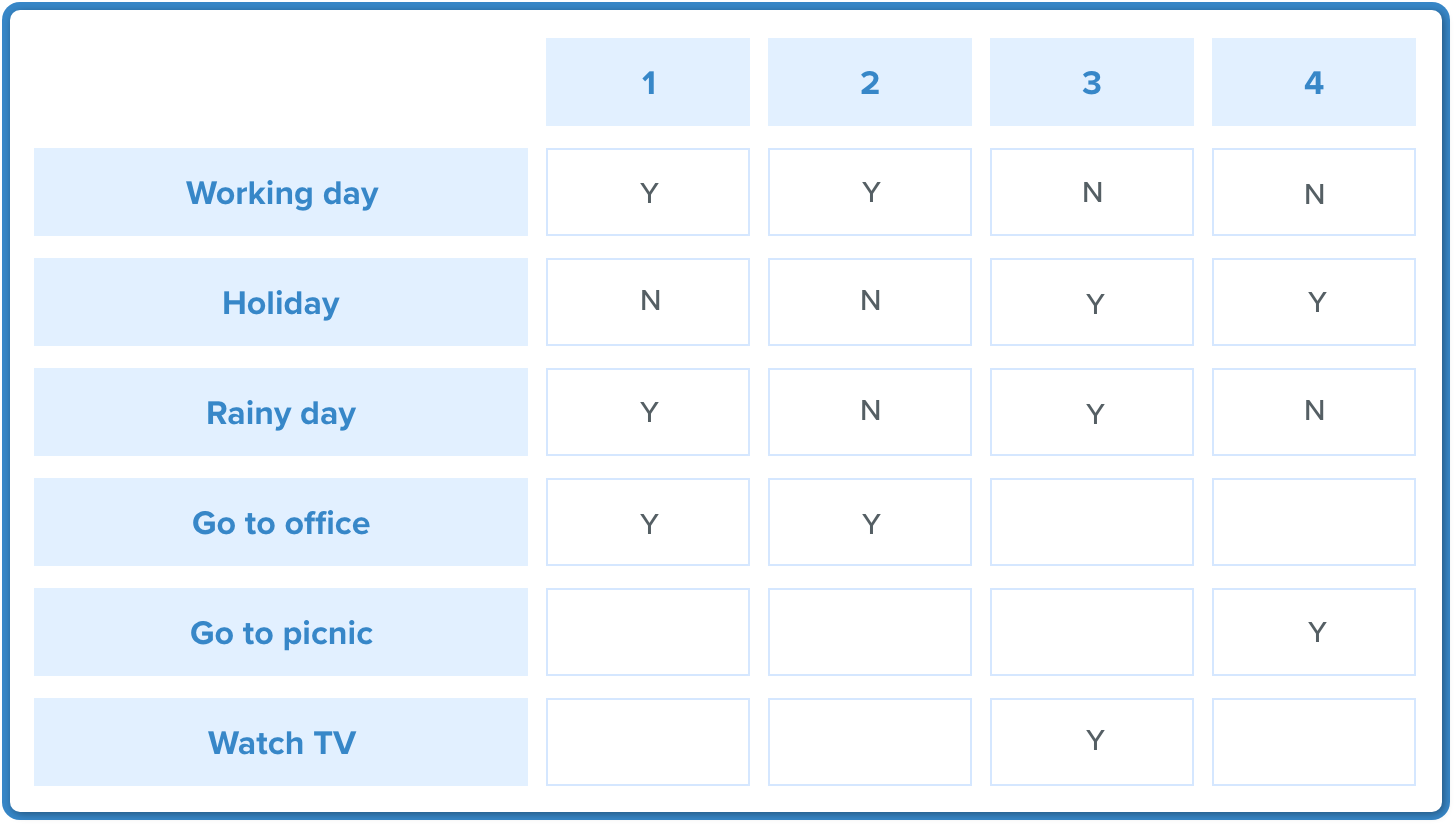
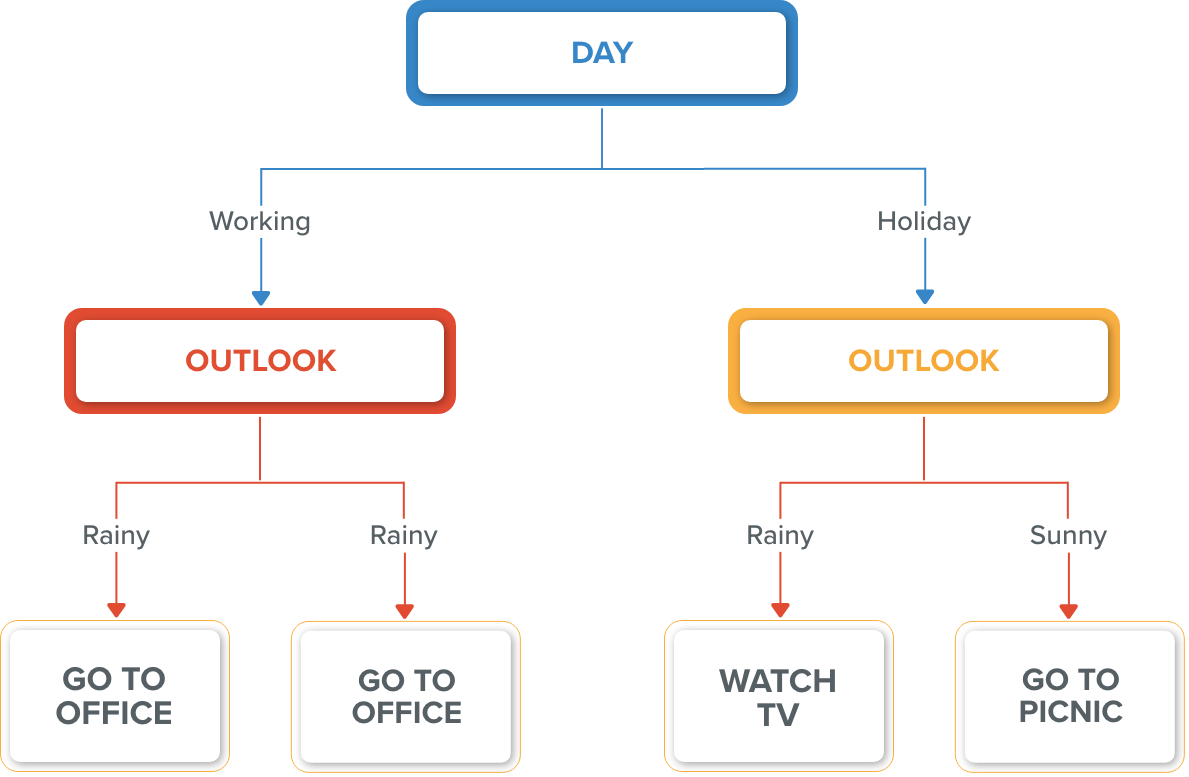
So Outlook = Rainy and Outlook = Sunny. The following rules are the optimized versions of the previous rules R1 and R2.
- R1 optimized: If (Day = Working) Then Go To Office
- R2 optimized: If (Day = Working) Then Go To Office
The refinement/optimization step produces rules that are effective, efficient, and accurate.
- State Transition Table Technique
State transition testing is used when some aspect of the system can be described using a 'finite state machine'.
This simply means that the system can exist in a finite number of states, and the transitions between them are determined by the machine's rule. This is the model that the system and tests are based on. A finite state system is any system in which the output varies depending on what has happened previously. A state diagram is a common representation of a finite state system.
If you ask for ₹100 from a bank ATM, you will be given cash. You may later make the same request but be denied the funds (because your balance is insufficient).
This refusal is due to the fact that the balance in your bank account has dropped from sufficient to cover the withdrawal to insufficient. The earlier withdrawal is most likely what caused your account to change state.
A state diagram can depict a model from the perspective of the system, an account, or a customer.
A state transition model is made up of four basic components:
- the states that the software may occupy (open/closed or funded/insufficient funds)
- the transitions from one state to another (not all transitions are allowed)
- the events that cause a transition (closing a file or withdrawing money)
- the actions that result from a transition (an error message or being given your cash)
It is important to note that in any given state, one event can only cause one action, but the same event from a different state can cause a different action and a different end state.
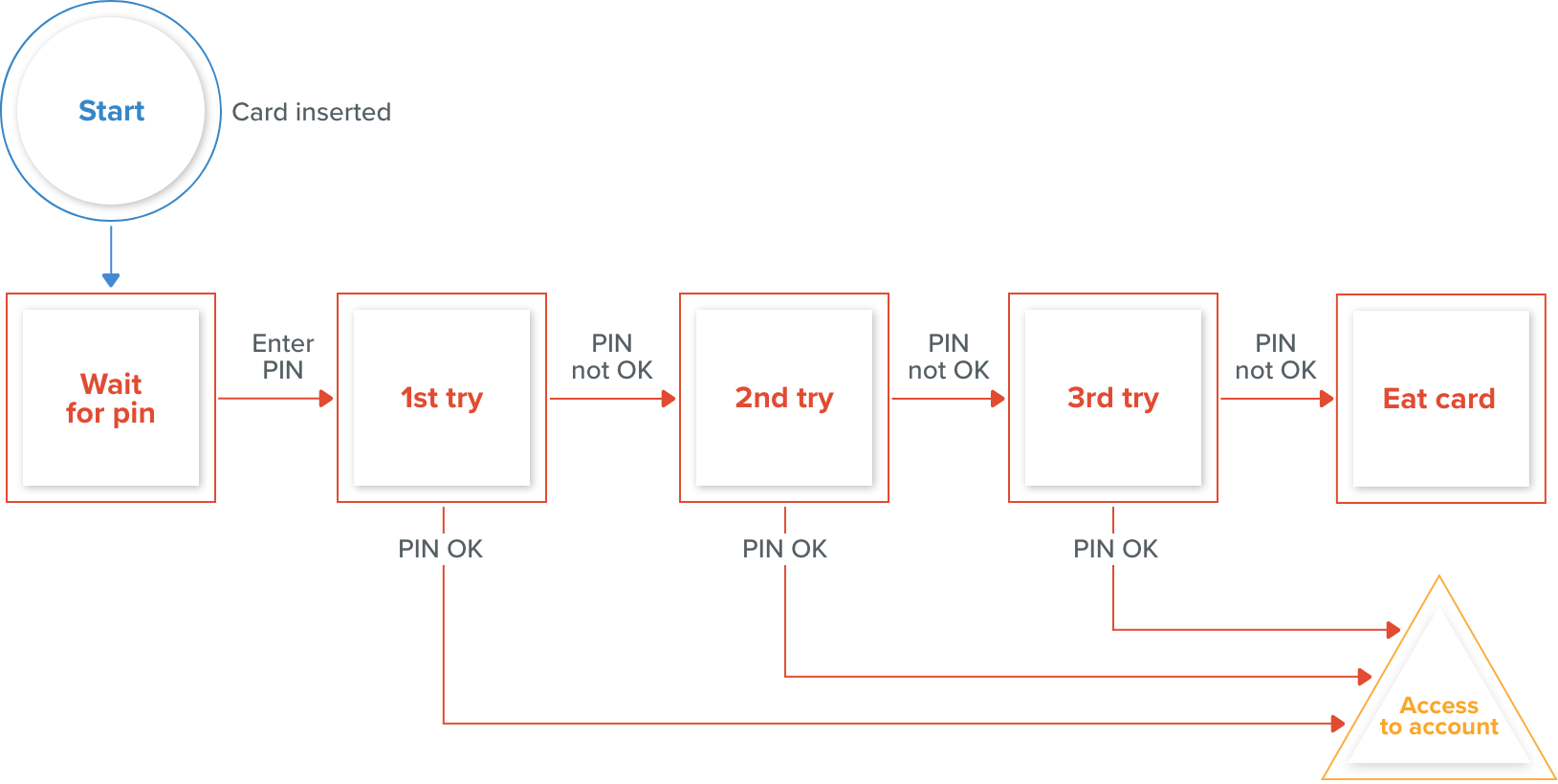
An example of entering a Personal Identification Number (PIN) into a bank account is shown above.
The states are represented by circles, transitions by lines with arrows, and events by text near the transitions.
The state diagram depicts seven states but only four events (card inserted, enter a PIN, valid PIN, and invalid PIN).
There would also be a return from the 'Eat card' state to the initial state.
There would be a 'cancel' option from 'wait for PIN' and the three tries, which would also reset the card to its initial state and eject it. The 'access account' state would mark the start of a new state diagram displaying the valid transactions that could now be performed on the account.
Use Case Testing Tests
The use case is a functional test of black box testing that is used to identify test cases from the beginning to the end of the system based on the system's usage. The team uses this technique to create a test scenario that can exercise the entire software based on the performance of each function from start to finish.
It is a graphical representation of business requirements that describes how the end user will interact with the software or application. The use cases provide us with all of the possible techniques for how the end-user will use the application, as shown in the image below:
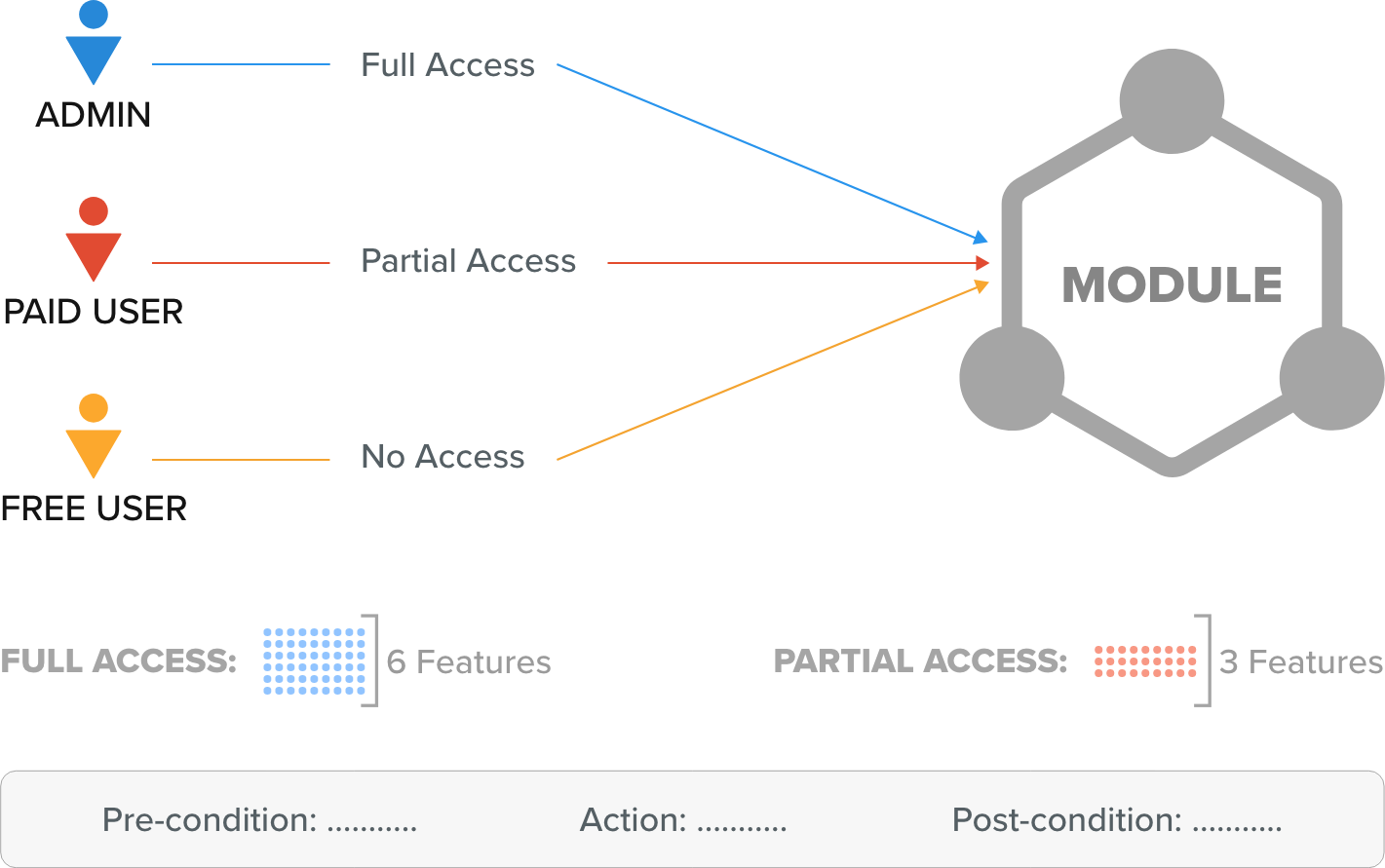
The image above shows a sample of a use case with a condition related to the customer requirement specification (CRS).
We have six different features for the software's module P.
And in this case, the Admin has access to all six features, the paid user has access to three features, and the Free user has no access to any of the features.
As with Admin, the various conditions are as follows:
- Pre-condition→ Admin must be generated
- Action→ Login as Paid user
- Post-condition→ 3 features must be present
- And for Free users, the different conditions would be as below:
- Pre-condition→ free user must be generated
- Action→ Login as a free user
- Post-condition→ no features
Who writes the use case?
The client supplies the customer requirement specification (CRS) for the application, and the development team drafts the use case in accordance with the CRS and then sends the use case to the client for review.
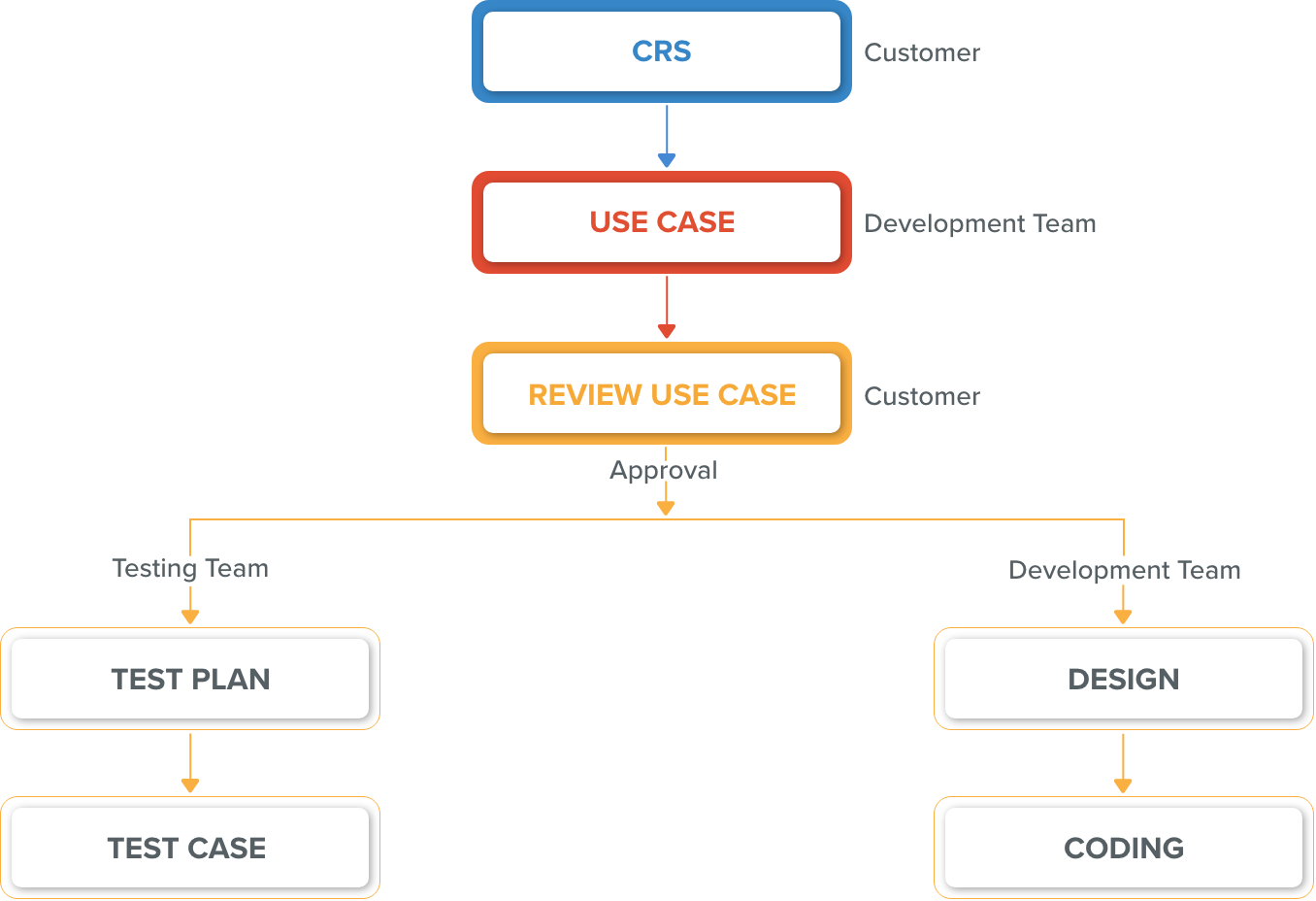
After the client’s approval, developers design and code the software, and the testing team writes test plans, and test cases for various software features.
Test design techniques benefits include:
There are several benefits of the test design techniques, Let’s discuss them briefly.
- Efficient use of time and resources: Test design techniques help testers to identify the most important and relevant test cases that need to be executed. This makes the testing process more efficient and saves time and resources.
- Improved test coverage: By using various test design techniques, testers can ensure that all the important features and functionality of the software are thoroughly tested. This improves test coverage and reduces the likelihood of defects being missed.
- Better defect detection: Test design techniques help testers to identify potential defects early in the testing process. This allows developers to fix the issues before they become more difficult and costly to resolve.
- Increased test effectiveness: Test design techniques allow testers to design tests that are more effective in identifying defects. This leads to higher-quality software and improved customer satisfaction.
- Consistent testing: Test design techniques provide a structured approach to designing tests that ensure that each test is executed consistently.
Black Box Testing Vs White Box Testing
While both black box and white box testing ensure a flawless end product, It's important to understand what is the underlying difference between the two.
|
Black Box Texting |
White Box Texting |
|
Performed by Software Testers |
Performed by Software Developers |
|
Software Implementation knowledge is not required |
Software Implementation Knowledge is required |
|
This approach treats the software as a black box, meaning the tester focuses only on the software's functionality and does not consider its internal structure, code, or design |
This approach tests the software's internal code, design, and architecture |
|
Coding knowledge is not necessary |
Coding knowledge is a must |
|
Test the software from the end user's perspective |
Focuses on testing the entire system, not just from the user’s side |
To sum up
Black box testing is used to find errors in the system without peering into the actual code. As mentioned above, it’s an efficient way to test larger code segments. This type of testing is often used to verify the quality and reliability of a system or application, by focusing on the user’s view of the system.
With emerging technological trends you need a partner that makes sure your website is innovative and user-friendly. At OpenSenseLabs, we help enterprises provide a better digital experience. Contact us at [email protected] and let our experts help you out.
Subscribe
Related Blogs
Workforce Management Tool: Features, Benefits & Complete Guide
“Simply Manage is a workforce management tool designed to streamline workflows across teams, making time tracking, resource…
Trek n Tech Annual Retreat 2025: A 7-Day Workcation of OSL

OSL family came together for the Trek n Tech Annual Retreat 2025, a 7-day workcation set amidst the serene beauty of…
Exploring Drupal's Single Directory Components: A Game-Changer for Developers
Web development thrives on efficiency and organisation, and Drupal, our favourite CMS, is here to amp that up with its…